Using a heartbeat as a sort of password
Implanted medical devices are so common that, in the future, devices will be vulnerable to hackers
Fred Dufour / AFP / Getty Images
Share
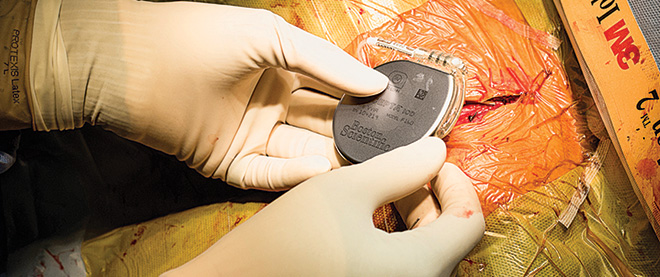
More people than ever have medical implants in their bodies, from cardiac defibrillators and pacemakers to insulin pumps. Implanted medical devices are so common that, in the future, some of these devices will be vulnerable to hackers.
“It’s fairly easy to bypass the access controls on medical implants,” says Ari Juels, a Boston-based expert in device security. Working with Farinaz Koushanfar and Masoud Rostami of Rice University, he developed a way to cut the risk of hacking into a medical device—by using the patient’s own heartbeat as a sort of password.
Of course, using a password of letters and numbers (as we do to protect our email accounts, online banking and WiFi routers) sounds much simpler. But in the event of an emergency, “there’s no assurance that medical personnel will know where to look for that password,” Juels says. With his system, to access an implant, they’d touch the patient with a device called a programmer, which would receive an electrocardiogram signature from the heart. If the signals captured by the programmer and the implant matched in that same instant, access would be granted. “The heart is generating random bits on a continuous basis,” Juels says. In other words, the password is different each time, yet it remains recognizable.
Juels thinks it’s inevitable that security like this will be introduced to medical implants, especially as a greater variety of more powerful devices is introduced. (For example, scientists are developing deep-brain-stimulation implants to treat depression and obsessive compulsive disorder.)
Security “is a pressing problem,” he says. “These devices have already become an inextricable part of our lives.”